- 3rd Jul, 2023
- Rinkal J.
Machine Learning vs Rule-Based Security in Cybersecurity
16th Mar, 2026 | Shailvi G.
- Cybersecurity

In today’s fast-evolving digital world, cybersecurity is no longer just an IT concern it’s a business survival strategy. From startups to global enterprises, everyone is facing increasingly sophisticated cyber threats.
And this brings us to a crucial question: Should you rely on traditional rule-based security systems, or is machine learning the future of cybersecurity?
Let’s break it down in a simple, conversational way so you can understand what works best and why.
Understanding Rule-Based Security
Before we jump into the buzz around machine learning, let’s first understand what rule-based security actually is.
Rule-based systems are exactly what they sound like they operate based on predefined rules. For example:
- Block IP addresses from certain regions
- Flag emails with suspicious keywords
- Deny access after multiple failed login attempts
These rules are manually created by cybersecurity experts based on known threats.
Why Rule-Based Security Was Popular
For years, rule-based systems were the backbone of cybersecurity because they are:
- Easy to implement
- Predictable
- Transparent in decision-making
Organizations knew exactly why something was blocked it matched a rule.
But Here’s the Problem…
Cyber threats today are no longer predictable. Hackers constantly evolve their tactics, making static rules less effective.
Rule-based systems:
- Can’t detect unknown threats
- Require constant manual updates
- Struggle with large-scale data
In short, they’re reactive not proactive.
What is Machine Learning in Cybersecurity?
Now let’s talk about machine learning, the game-changer in cybersecurity.
Machine learning is a subset of artificial intelligence that enables systems to learn from data and improve over time without being explicitly programmed.
Instead of relying on fixed rules, machine learning models:
- Analyze patterns
- Detect anomalies
- Predict potential threats
Think of it like a smart security guard who learns from every incident and becomes better over time.
How Machine Learning Works in Cybersecurity
Machine learning models are trained on massive datasets that include both normal and malicious behavior.
Here’s how it typically works:
- Data Collection: Logs, network traffic, user behavior
- Training the Model: Identify patterns and anomalies
- Real-Time Monitoring: Detect suspicious activity instantly
- Continuous Learning: Improve accuracy over time
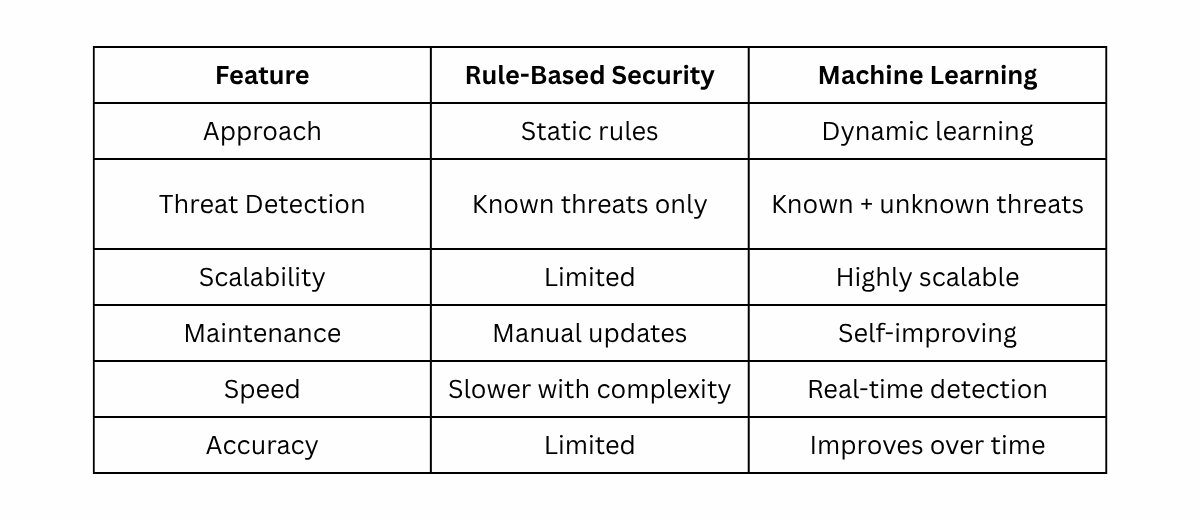
Key Differences: Machine Learning vs Rule-Based Security
Let’s compare both approaches side by side.
Where Rule-Based Security Still Works
Despite its limitations, rule-based security is not obsolete.
It still works well in:
- Compliance-based environments
- Basic firewall rules
- Simple access controls
- Small businesses with limited risk exposure
For example, blocking a known malicious IP doesn’t require machine learning, it’s straightforward.
Where Machine Learning Shines
Machine learning excels in complex and dynamic environments where threats evolve rapidly.
1. Detecting Zero-Day Attacks
Zero-day attacks exploit vulnerabilities that are not yet known. Rule-based systems fail here because there’s no rule for something new.
Machine learning, however, detects unusual behavior even if it’s never seen before.
2. Behavioral Analysis
Machine learning tracks user behavior:
- Login patterns
- Device usage
- Data access
If something unusual happens like logging in from a new country it raises an alert.
3. Fraud Detection
Banks and fintech companies rely heavily on machine learning to detect fraudulent transactions in real time.
4. Threat Intelligence
Machine learning systems can analyze global threat data and adapt quickly.
Challenges of Machine Learning in Cybersecurity
Now, let’s not pretend machine learning is perfect. It comes with its own set of challenges:
1. Data Dependency
Machine learning models need large amounts of quality data to perform well.
2. Complexity
They are harder to implement compared to rule-based systems.
3. False Positives
Sometimes, unusual but harmless behavior gets flagged.
4. Cost
Initial setup and infrastructure can be expensive.
The Hybrid Approach: Best of Both Worlds
Here’s the reality most organizations today are not choosing one over the other.
They are combining both approaches.
Why Hybrid Works
- Rule-based systems handle known threats
- Machine learning detects unknown threats
This layered approach creates a stronger cybersecurity framework.
Real-World Example
Imagine a company’s security system:
- A rule-based system blocks known malware signatures
- A machine learning model detects unusual data transfers
Together, they create a robust defense mechanism.
How Bombay Softwares is Leveraging Artificial Intelligence
At Bombay Softwares, the focus is not just on adopting technology but building intelligent solutions that solve real business problems.
The company is actively working on advanced artificial intelligence and machine learning models to enhance cybersecurity, automation, and data-driven decision-making.
Their approach involves:
- Developing scalable AI-driven platforms
- Integrating machine learning into enterprise workflows
- Building predictive analytics systems
- Enhancing threat detection capabilities
By combining deep technical expertise with real-world use cases, Bombay Softwares is helping businesses transition from traditional systems to intelligent, future-ready solutions.
If you want to explore how machine learning is transforming other domains like marketing.
Why Machine Learning is the Future of Cybersecurity
Let’s be honest, cyber threats are getting smarter every day. And to fight smart threats, you need smarter systems.
Machine learning offers:
- Proactive threat detection
- Faster response times
- Scalable security solutions
- Continuous improvement
According to this detailed overview by Palo Alto Networks. Machine learning is becoming a core component of modern cybersecurity strategies.
So, Which One Should You Choose?
If you’re still wondering whether to go with rule-based security or machine learning, here’s a simple answer:
- Small systems or basic protection? → Rule-based works.
- Large-scale, dynamic environments? → Machine learning is essential.
- Best security posture? → Use both
Final Thoughts
Cybersecurity is no longer about building walls it’s about building intelligent defense systems.
Rule-based security gave us a strong foundation, but it’s no longer enough on its own. Machine learning is stepping in to fill the gaps, offering adaptability, speed, and intelligence.
The future lies in combining human expertise, rule-based logic, and machine learning capabilities to create a resilient cybersecurity ecosystem.
As businesses continue to digitize, adopting machine learning in cybersecurity is not just an option it’s a necessity.
More blogs in "Cybersecurity"
- 17th Jul, 2023
- Rinkal J.
Unleashing the Potential of Digital Trust: Driving Business Transformation
- 25th Sep, 2024
- Aanya G.
Cybersecurity: The Year of Deception Unveiled at GITEX 2024
Join our Newsletter
Get insights on the latest trends in technology and industry, delivered straight to your inbox.